IoT: Living at the edge
Greetings from Viper, trusted partner for your AI journey. This AI-generated hummingbird has been busy buzzing around in the clouds, figuring out how companies can…
From Our CEO

OpenText Committed to Climate Innovation

The Future Needs You Today: A Conversation on AI & Decolonization with Karen Palmer

OpenText World 2023—Welcome to the AI Revolution
Discover
Insight is the new GOLD
My children will never face the challenges that I did. No television, no personal cell phones, and don’t ask me about my first computer (which…
April 17, 2024 • 4 minutes readTransforming digital forensic investigations
In the modern landscape of digital forensics, investigators must navigate many challenges stemming from the exponential growth of digital data.
April 15, 2024 • 4 minutes readAccelerating Data Insights: Unleash the Power of OpenText Axcelerate with Aviator
Introducing Legal Tech Aviator – the central AI nervous system of our smart legal platform
April 15, 2024 • 3 minutes readTop 5 predictions for manufacturing in 2024
In recent years, the manufacturing sector has experienced notable disruptions – including supply chain instability, product demand fluctuations, transportation issues, and workforce shortages. However, amidst…
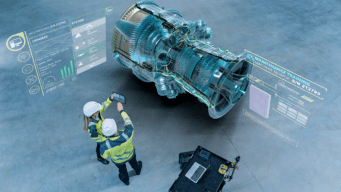
December 11, 2023 • 6 minutes readSupercharge manufacturing operations
Product Lifecycle Management (PLM) systems hold the definitive version of the truth for released product design and development information. Manufacturing operations across high-tech, industrial and…
August 07, 2023 • 5 minutes readWhat is product information management?
Product information is the backbone of the manufacturing industry. Released product data, documents and drawings are of critical importance throughout the manufacturing value chain, from…
August 03, 2023 • 4 minutes readTransforming digital forensic investigations
In the modern landscape of digital forensics, investigators must navigate many challenges stemming from the exponential growth of digital data.
April 15, 2024 • 4 minutes readNavigating the Intersection of AI and Financial Risk: A Proactive Approach
Don’t miss out on the opportunity to transform your organization’s approach to data security, privacy, and governance in the age of GenAI.
April 02, 2024 • 3 minutes readCorporate treasuries are going digital with bank solutions
This is the third of our four-part series on modernizing treasury departments. In the first installment we discussed how to automate basic treasury functions and…
March 07, 2024 • 3 minutes readTop 5 information management predictions for energy and utility sector in 2024
Hello from Alaska! The world is in a race for energy, and that race is just as much about information management as it is about…
November 09, 2023 • 5 minutes readMaking smart grids, smart fields, and smart facilities smarter with OpenText
The world is in a race for energy. Energy companies today are striving to create intelligent, connected, secure, responsible and scalable enterprises. Smart grids, smart oilfields,…
July 26, 2023 • 4 minutes readWorking smarter with Smart Checklists and Forms
The energy sector, and closely related industries such as chemicals and metals and mining, are asset-intensive industries. This means that revenue is generated from assets…
July 13, 2023 • 5 minutes readRetail and CPG companies to focus on intelligence, engagement, and security in 2024
The retail industry has always been at the forefront of technological innovation, constantly adapting to meet the evolving needs of consumers. As we step into…
December 01, 2023 • 4 minutes readJ. Renee Group Steps up seasonal sales
For more than 45 years, J. Renee Group has designed and manufactured bold footwear styles across a range of categories, including comfort, casual dress, dress,…
October 26, 2023 • 4 minutes read2023 retail and consumer goods industry predictions
The retail and consumer goods industries continue to evolve at a rapid rate. Overall, 2022 retail holiday spending grew 7. 6%, according to Mastercard SpendingPulse. …
January 05, 2023 • 4 minutes readTransforming digital forensic investigations
In the modern landscape of digital forensics, investigators must navigate many challenges stemming from the exponential growth of digital data.
April 15, 2024 • 4 minutes readThe total patient experience: reflections from HIMSS 2024
The landscape of healthcare is evolving rapidly, driven by shifting consumer expectations and technological advancements. Patients are no longer passive recipients of care; they are…
March 26, 2024 • 4 minutes readThe Change Healthcare Cyberattack: A Wake-Up Call for Healthcare Cybersecurity
The attack on Change Healthcare is a pivotal moment for healthcare cybersecurity.
March 21, 2024 • 3 minutes readGE Lighting, a Savant company, switches up its approach to supplier collaboration
Our journey began at the turn of the century when Thomas Edison invented the carbon filament lamp. Today, GE Lighting, a Savant company, is taking the…
February 08, 2024 • 4 minutes readTop 5 predictions for manufacturing in 2024
In recent years, the manufacturing sector has experienced notable disruptions – including supply chain instability, product demand fluctuations, transportation issues, and workforce shortages. However, amidst…
December 11, 2023 • 6 minutes readManufacturers turning to cloud based B2B integration but there are challenges ahead
Recent disruptions have exposed the fragility of the global supply chain, and manufacturers have suffered more than most. Manufacturing organizations are now looking towards digital…
October 30, 2023 • 6 minutes readNavigating the Intersection of AI and Financial Risk: A Proactive Approach
Don’t miss out on the opportunity to transform your organization’s approach to data security, privacy, and governance in the age of GenAI.
April 02, 2024 • 3 minutes readThe Change Healthcare Cyberattack: A Wake-Up Call for Healthcare Cybersecurity
The attack on Change Healthcare is a pivotal moment for healthcare cybersecurity.
March 21, 2024 • 3 minutes read4 hidden benefits of generative AI in DevOps
Large-scale, generative AI models are opening up the possibility to do anything—from building applications to designing game-changing UI experiences. And as generative AI continues to…
February 20, 2024 • 4 minutes readAccelerating Data Insights: Unleash the Power of OpenText Axcelerate with Aviator
Introducing Legal Tech Aviator – the central AI nervous system of our smart legal platform
April 15, 2024 • 3 minutes readWhat’s new in OpenText Axcelerate
The latest announcement by OpenText of Cloud Editions includes some great updates to OpenText™ Axcelerate™. Check out the latest updates below. January 2024: What’s new…
January 31, 2024 • 20 minutes readThe evolving role of general counsel: Securing a seat at the table
Technological, social, and economic events have changed the legal and regulatory landscape. There was a time when in-house legal departments and the general counsel had…
January 17, 2024 • 7 minutes readTop content management predictions for 2024
As 2023 draws to a close, at OpenText, we’re reflecting on the year behind us, and the remarkable advancements made in how we use information…
December 14, 2023 • 7 minutes readTop information management trends for life sciences in 2024
The life sciences industry has seen monumental change over the past few years. From the Covid-19 pandemic to a spike in investment, coupled with rising…
November 30, 2023 • 5 minutes readAssembling the pieces: Archiving and retention in Life Sciences
In the world of pharmaceuticals, something interesting keeps happening—companies acquire, merge, or divest from other companies. It’s like a puzzle they’re trying to solve getting…
September 21, 2023 • 4 minutes readOpenText Summit | Houston Energy 2024 summary & key takeaways
A deep dive into the future of energy operations with AI
March 22, 2024 • 10 minutes readHow fast can you access vital asset documentation?
The world is in a race for energy and that race is just as much about information management as it is energy itself. Trillions of…
January 09, 2024 • 3 minutes readTop 5 information management predictions for energy and utility sector in 2024
Hello from Alaska! The world is in a race for energy, and that race is just as much about information management as it is about…
November 09, 2023 • 5 minutes readTransforming digital forensic investigations
In the modern landscape of digital forensics, investigators must navigate many challenges stemming from the exponential growth of digital data.
April 15, 2024 • 4 minutes readNavigating the Intersection of AI and Financial Risk: A Proactive Approach
Don’t miss out on the opportunity to transform your organization’s approach to data security, privacy, and governance in the age of GenAI.
April 02, 2024 • 3 minutes read5 highlights from the OpenText Government Summit
Key learnings we took away from this year’s 2024 OpenText Government Summit
March 21, 2024 • 7 minutes readHow Pick n Pay plans to transform software test cases with AI
Beta tester reports OpenText DevOps Aviator delivers fast, accurate results
April 05, 2024 • 5 minutes readLoxam boosts customer service and environmental sustainability with faster document workflows
As the leading equipment rental provider in Europe, Loxam offers construction firms everything from powered access systems to earthmoving machinery. We own a fleet of…
March 06, 2024 • 4 minutes readManutan combines digital services with the human touch to delight customers
At Manutan, we equip businesses and communities with the products and services they require to succeed. Headquartered in France, our company has three divisions, serving…
January 31, 2024 • 4 minutes readOpenText Summit | Houston Energy 2024 summary & key takeaways
A deep dive into the future of energy operations with AI
March 22, 2024 • 10 minutes readHow fast can you access vital asset documentation?
The world is in a race for energy and that race is just as much about information management as it is energy itself. Trillions of…
January 09, 2024 • 3 minutes readTop 5 information management predictions for energy and utility sector in 2024
Hello from Alaska! The world is in a race for energy, and that race is just as much about information management as it is about…
November 09, 2023 • 5 minutes readHow green is your application delivery software?
Sustainability is a growing priority for businesses and customers alike. As companies focus on their sustainability and environmental social governance (ESG) impacts, the IT landscape…
April 22, 2024 • 3 minutes readWhat’s new in OpenText Core Content
OpenText™ Core Content is a fast-deploying cloud content management solution that delivers simple, agile and secure cloud-based content management. It integrates into crucial business process…
April 19, 2024 • 9 minutes readWhat’s new in OpenText Business Network Cloud
The latest announcement by OpenText of Cloud Editions includes exciting updates to the OpenText™ Business Network Cloud. Check out the latest updates below. April 2024:…
April 15, 2024 • 3 minutes readDrive customer success with OpenText Experience Cloud 24.2
Customers are at the heart of every thriving business.
April 15, 2024 • 4 minutes readImpact of agent experience management on customer success and service
Customer success and customer service are two interconnected functions inside a business. Both are focused on ensuring customer satisfaction and loyalty but they have some…
April 08, 2024 • 4 minutes readThree customer success trends in a post-pandemic world
COVID-19 changed everything. Loyalty is on the auction block. Customers are uncertain: delaying purchases and shopping around. Brands that win in this new era will…
April 04, 2024 • 4 minutes readNavigating the Intersection of AI and Financial Risk: A Proactive Approach
Don’t miss out on the opportunity to transform your organization’s approach to data security, privacy, and governance in the age of GenAI.
April 02, 2024 • 3 minutes readCorporate treasuries are going digital with bank solutions
This is the third of our four-part series on modernizing treasury departments. In the first installment we discussed how to automate basic treasury functions and…
March 07, 2024 • 3 minutes readHow to choose the right financial technology partner
Selecting the right financial technology partner is a decision that carries long-lasting implications for banks’ success and future resilience, no matter the size. The dynamic…
February 01, 2024 • 4 minutes readWhat’s new in OpenText Extended ECM for SAP SuccessFactors
We’re thrilled to share some fantastic enhancements that will make your experience with OpenText™ SAP® SuccessFactors® even more seamless and powerful. Here are 7 ‘What’s…
February 06, 2024 • 2 minutes readTop content management predictions for 2024
As 2023 draws to a close, at OpenText, we’re reflecting on the year behind us, and the remarkable advancements made in how we use information…
December 14, 2023 • 7 minutes readThriving in HR: Celebrating Achievements and Navigating Challenges
In HR’s ever-evolving landscape, staying ahead by using technology is imperative in facilitating change. During our recent OpenText customer roundtable on 31st October 2023, a…
December 12, 2023 • 4 minutes readHow green is your application delivery software?
Sustainability is a growing priority for businesses and customers alike. As companies focus on their sustainability and environmental social governance (ESG) impacts, the IT landscape…
April 22, 2024 • 3 minutes readWhat’s new in OpenText Core Content
OpenText™ Core Content is a fast-deploying cloud content management solution that delivers simple, agile and secure cloud-based content management. It integrates into crucial business process…
April 19, 2024 • 9 minutes readTransforming digital forensic investigations
In the modern landscape of digital forensics, investigators must navigate many challenges stemming from the exponential growth of digital data.
April 15, 2024 • 4 minutes readAccelerating Data Insights: Unleash the Power of OpenText Axcelerate with Aviator
Introducing Legal Tech Aviator – the central AI nervous system of our smart legal platform
April 15, 2024 • 3 minutes readWhat’s new in OpenText Axcelerate
The latest announcement by OpenText of Cloud Editions includes some great updates to OpenText™ Axcelerate™. Check out the latest updates below. January 2024: What’s new…
January 31, 2024 • 20 minutes readThe evolving role of general counsel: Securing a seat at the table
Technological, social, and economic events have changed the legal and regulatory landscape. There was a time when in-house legal departments and the general counsel had…
January 17, 2024 • 7 minutes readDrive customer success with OpenText Experience Cloud 24.2
Customers are at the heart of every thriving business.
April 15, 2024 • 4 minutes readImpact of agent experience management on customer success and service
Customer success and customer service are two interconnected functions inside a business. Both are focused on ensuring customer satisfaction and loyalty but they have some…
April 08, 2024 • 4 minutes readThree customer success trends in a post-pandemic world
COVID-19 changed everything. Loyalty is on the auction block. Customers are uncertain: delaying purchases and shopping around. Brands that win in this new era will…
April 04, 2024 • 4 minutes readOpenText Summit | Houston Energy 2024 summary & key takeaways
A deep dive into the future of energy operations with AI
March 22, 2024 • 10 minutes readLoxam boosts customer service and environmental sustainability with faster document workflows
As the leading equipment rental provider in Europe, Loxam offers construction firms everything from powered access systems to earthmoving machinery. We own a fleet of…
March 06, 2024 • 4 minutes readHow fast can you access vital asset documentation?
The world is in a race for energy and that race is just as much about information management as it is energy itself. Trillions of…
January 09, 2024 • 3 minutes readOpenText reimagines work with smarter information at Google Cloud Next ‘24
Great AI starts with great information management The Cognitive Era is upon us, with 92% of U.S. businesses set to implement AI into their operations…
April 02, 2024 • 4 minutes readOptimize the sales experience with a complete customer view
As the digital landscape for sales teams has shifted over recent years, so too have consumer expectations. Customers are used to the convenience and speed…
January 29, 2024 • 2 minutes readElevating contact center excellence
Contact centers face persistent challenges in ensuring optimal agent productivity and efficiency. OpenText™ Qfiniti Explore 24.1 emerges as a beacon of innovation, addressing the pressing…
January 23, 2024 • 2 minutes readNavigating the Intersection of AI and Financial Risk: A Proactive Approach
Don’t miss out on the opportunity to transform your organization’s approach to data security, privacy, and governance in the age of GenAI.
April 02, 2024 • 3 minutes readCybersecurity Services combat an APT with NDR
Attackers linked to Iran and China are actively targeting critical infrastructure. Both the U.S. Environmental Protection Agency and National Security Agency have requested that each…
March 28, 2024 • 4 minutes readOpenText Summit | Houston Energy 2024 summary & key takeaways
A deep dive into the future of energy operations with AI
March 22, 2024 • 10 minutes readWhat’s new in OpenText Business Network Cloud
The latest announcement by OpenText of Cloud Editions includes exciting updates to the OpenText™ Business Network Cloud. Check out the latest updates below. April 2024:…
April 15, 2024 • 3 minutes readDitch one-size-fits-all: OpenText offers customizable Microsoft Dynamics 365 EDI integration
A Microsoft-certified Dynamics 365 adapter delivers reliable on-time and on-budget EDI integration, surpassing inflexible alternative solutions
April 10, 2024 • 3 minutes reade-Invoicing mandates and updates: Germany
March 2024 German Federal Council officially approves law driving the e-Invoicing mandate On 22nd March 2024 The German Bundesrat – the Federal Council – officially…
March 22, 2024 • 10 minutes readDriving success on the historic Monaco Circuit
OpenText real-time data analytics powers Jaguar TCS Racing
April 25, 2024 • 4 minutes readMachine vs. machine
Greetings from Mav, trusted partner for your AI journey. This AI-generated moose has been on the hunt for threats and keeping security top of mind….
April 19, 2024 • 4 minutes readNext-gen developer experience
Greetings from Goose, a trusted partner for your AI journey. This AI-generated goose has been the champion of seven-star experiences, and over the last few…
April 19, 2024 • 5 minutes readAn inside look at enterprise document accessibility for PDFs
Accessible PDFs are easy to use – enabling most people to view, read or interact with them. The goal is to create an inclusive experience…
February 08, 2024 • 4 minutes readZeroing-In on Zero Hunger
At OpenText, we believe that the future of growth is sustainable and inclusive. We also believe that one of the best ways we can make…
January 08, 2024 • 7 minutes readHonoring the National Day for Truth and Reconciliation at OpenText
Last month, OpenText joined millions of Canadians in recognizing the third annual National Day for Truth and Reconciliation, a day to honor the First Nations,…
October 31, 2023 • 5 minutes reade-Invoicing mandates and updates: Germany
March 2024 German Federal Council officially approves law driving the e-Invoicing mandate On 22nd March 2024 The German Bundesrat – the Federal Council – officially…
March 22, 2024 • 10 minutes reade-Invoicing mandates and updates: Malaysia
February 2024 Malaysia’s clearance e-Invoicing mandate – what we know so far Malaysia has joined the increasing number of countries to announce a new mandatory…
March 06, 2024 • 3 minutes reade-Invoicing mandates and updates: France
February 2024: To PDP, or not to PDP, that is the question
March 04, 2024 • 16 minutes readDriving success on the historic Monaco Circuit
OpenText real-time data analytics powers Jaguar TCS Racing
April 25, 2024 • 4 minutes readOpenText World Europe 2024 has taken flight
AI: Elevating human potential
April 15, 2024 • 5 minutes readElevate human potential with Cloud Editions (CE) 24.2
Latest innovations revealed at OpenText World Europe 2024
April 15, 2024 • 10 minutes readSparking 25,000 Career Conversations
In early March, OpenText held Career Week, one of our most highly anticipated annual employee events.
April 08, 2024 • 5 minutes readZeroing-In on Zero Hunger
At OpenText, we believe that the future of growth is sustainable and inclusive. We also believe that one of the best ways we can make…
January 08, 2024 • 7 minutes readHonoring the National Day for Truth and Reconciliation at OpenText
Last month, OpenText joined millions of Canadians in recognizing the third annual National Day for Truth and Reconciliation, a day to honor the First Nations,…
October 31, 2023 • 5 minutes readMachine vs. machine
Greetings from Mav, trusted partner for your AI journey. This AI-generated moose has been on the hunt for threats and keeping security top of mind….
April 19, 2024 • 4 minutes readNext-gen developer experience
Greetings from Goose, a trusted partner for your AI journey. This AI-generated goose has been the champion of seven-star experiences, and over the last few…
April 19, 2024 • 5 minutes readIoT: Living at the edge
Greetings from Viper, trusted partner for your AI journey. This AI-generated hummingbird has been busy buzzing around in the clouds, figuring out how companies can…
April 19, 2024 • 4 minutes readWhat’s new in OpenText Core Content
OpenText™ Core Content is a fast-deploying cloud content management solution that delivers simple, agile and secure cloud-based content management. It integrates into crucial business process…
April 19, 2024 • 9 minutes readElevate human potential with Cloud Editions (CE) 24.2
Latest innovations revealed at OpenText World Europe 2024
April 15, 2024 • 10 minutes readWhat’s new in OpenText Business Network Cloud
The latest announcement by OpenText of Cloud Editions includes exciting updates to the OpenText™ Business Network Cloud. Check out the latest updates below. April 2024:…
April 15, 2024 • 3 minutes readCybersecurity Services combat an APT with NDR
Attackers linked to Iran and China are actively targeting critical infrastructure. Both the U.S. Environmental Protection Agency and National Security Agency have requested that each…
March 28, 2024 • 4 minutes readStrengthening Higher Education Institutions against evolving cyberthreats
As cyberthreats continue to evolve, it is crucial for higher education institutions and universities to be vigilant. Enforcing security strategies prudently designed to safeguard digital…
January 24, 2024 • 4 minutes readStrengthening cyber resilience
Cyberattacks are on track to cause $10.5 trillion a year in damage by 2025. That’s a 300 percent increase from 2015 levels. A robust cybersecurity…
December 19, 2023 • 4 minutes readDitch one-size-fits-all: OpenText offers customizable Microsoft Dynamics 365 EDI integration
A Microsoft-certified Dynamics 365 adapter delivers reliable on-time and on-budget EDI integration, surpassing inflexible alternative solutions
April 10, 2024 • 3 minutes readOpenText reimagines work with smarter information at Google Cloud Next ‘24
Great AI starts with great information management The Cognitive Era is upon us, with 92% of U.S. businesses set to implement AI into their operations…
April 02, 2024 • 4 minutes readCollaboration tools are critical for digital workplace success
The adage ‘two heads are better than one’ is just about always true. Enabling people to work well together is just smart business. Companies continue…
February 13, 2024 • 5 minutes readWhat’s new in Application Modernization & Connectivity
The latest OpenText™ Cloud Editions includes updates to AMC’s COBOL, Enterprise Suite and Host Connectivity offerings – designed to support IT leaders in their continuous…
July 24, 2023 • 3 minutes readOpenText reimagines work with smarter information at Google Cloud Next ‘24
Great AI starts with great information management The Cognitive Era is upon us, with 92% of U.S. businesses set to implement AI into their operations…
April 02, 2024 • 4 minutes readCollaboration tools are critical for digital workplace success
The adage ‘two heads are better than one’ is just about always true. Enabling people to work well together is just smart business. Companies continue…
February 13, 2024 • 5 minutes readConnect with OpenText at Google Cloud Next 2023
Google Cloud Next 2023 is back in-person on August 29-31, in San Francisco. This is Google’s largest annual event with more than 15,000 IT, line…
August 22, 2023 • 4 minutes readDitch one-size-fits-all: OpenText offers customizable Microsoft Dynamics 365 EDI integration
A Microsoft-certified Dynamics 365 adapter delivers reliable on-time and on-budget EDI integration, surpassing inflexible alternative solutions
April 10, 2024 • 3 minutes readExtend your information management flows with low code integrations
Many organizations have implemented content management platforms to automate their business processes but often fail to provide users with tools that increase employee productivity. Business…
April 24, 2023 • 5 minutes readFind new OpenText solutions on enterprise application marketplaces
It’s not just big retailers doing online business: 80% of sales will be digital transactions by 2025. As cloud adoption and digital business grows, customers increasingly…
February 16, 2023 • 4 minutes readSimplify your solution building with APIs at OpenText World 2022
Building, connecting, and extending applications that leverage the power of APIs has become the key to success for Developers all over the world. The OpenText™…
August 23, 2022 • 6 minutes readDeveloper solutions are the backbone of EHR applications
HealthTech companies that produce EHR (electronic health records) software for use in hospitals, clinics, and labs, have a moral (and legal) duty to ensure that…
July 12, 2022 • 3 minutes readKeep customer data streams clean with cloud capture from OpenText
Did you know that the average worker is using an average of nine apps in a day? This is just for routine tasks like invoice…
February 15, 2022 • 4 minutes readOptimize the sales experience with a complete customer view
As the digital landscape for sales teams has shifted over recent years, so too have consumer expectations. Customers are used to the convenience and speed…
January 29, 2024 • 2 minutes readOpenText & Salesforce help save the holidays with AI!
This holiday season Santa needs help checking his lists! Santa receives millions of wish list letters from children around the world, and he needs to…
December 15, 2023 • 2 minutes readTop things you may have missed at Dreamforce 23!
What an inspiring and epic Dreamforce, September 12-14, with the OpenText team! It was fantastic to connect with people and colleagues face to face to…
September 26, 2023 • 4 minutes readWhat’s new in OpenText Extended ECM for SAP SuccessFactors
We’re thrilled to share some fantastic enhancements that will make your experience with OpenText™ SAP® SuccessFactors® even more seamless and powerful. Here are 7 ‘What’s…
February 06, 2024 • 2 minutes readGlobal analyst firm names OpenText a leader in digital asset management
Billions of rich media assets are created every day for new and emerging channels. With all this creative, consistency is a challenge that goes right…
January 11, 2024 • 2 minutes readThriving in HR: Celebrating Achievements and Navigating Challenges
In HR’s ever-evolving landscape, staying ahead by using technology is imperative in facilitating change. During our recent OpenText customer roundtable on 31st October 2023, a…
December 12, 2023 • 4 minutes readInsight is the new GOLD
My children will never face the challenges that I did. No television, no personal cell phones, and don’t ask me about my first computer (which…
April 17, 2024 • 4 minutes readCybersecurity Services combat an APT with NDR
Attackers linked to Iran and China are actively targeting critical infrastructure. Both the U.S. Environmental Protection Agency and National Security Agency have requested that each…
March 28, 2024 • 4 minutes readTake the stress out of planning your training schedule
We’ve seen countless headlines over the past few years about the skills gap and the talent shortage. According to Forbes, “from increased job satisfaction and…
March 19, 2024 • 2 minutes readNavigating success
A collaborative journey
March 15, 2024 • 2 minutes readThe Power of L.O.V.E.
In the rapidly evolving landscape of Software-as-a-Service (SaaS), the role of customer success has become increasingly pivotal. Beyond simply providing reactive technical support, successful businesses…
February 14, 2024 • 4 minutes readThe customer success journey starts with L.O.V.E.
Purchasing technology for your enterprise, agency, or organization can be a long and exhausting journey. Once the contract has been signed, you’re ready to go,…
November 20, 2023 • 4 minutes readTake the stress out of planning your training schedule
We’ve seen countless headlines over the past few years about the skills gap and the talent shortage. According to Forbes, “from increased job satisfaction and…
March 19, 2024 • 2 minutes readWhat is Microlearning?
The name says it all, because microlearning refers to learning in small learning units. Instead of working with an extensive training manual or participating in…
February 01, 2024 • 3 minutes readGet flexible training options to meet all learning needs
You’ve identified a business problem, evaluated options, and invested in a new software solution to address the issue. In order to drive user adoption and…
January 09, 2024 • 4 minutes readInsight is the new GOLD
My children will never face the challenges that I did. No television, no personal cell phones, and don’t ask me about my first computer (which…
April 17, 2024 • 4 minutes readCybersecurity Services combat an APT with NDR
Attackers linked to Iran and China are actively targeting critical infrastructure. Both the U.S. Environmental Protection Agency and National Security Agency have requested that each…
March 28, 2024 • 4 minutes readStrengthening Higher Education Institutions against evolving cyberthreats
As cyberthreats continue to evolve, it is crucial for higher education institutions and universities to be vigilant. Enforcing security strategies prudently designed to safeguard digital…
January 24, 2024 • 4 minutes readDriving success on the historic Monaco Circuit
OpenText real-time data analytics powers Jaguar TCS Racing
April 25, 2024 • 4 minutes readHow green is your application delivery software?
Sustainability is a growing priority for businesses and customers alike. As companies focus on their sustainability and environmental social governance (ESG) impacts, the IT landscape…
April 22, 2024 • 3 minutes readGoing green with cloud fax
Transforming communication for a sustainable future
April 22, 2024 • 2 minutes readDriving success on the historic Monaco Circuit
OpenText real-time data analytics powers Jaguar TCS Racing
April 25, 2024 • 4 minutes readInsight is the new GOLD
My children will never face the challenges that I did. No television, no personal cell phones, and don’t ask me about my first computer (which…
April 17, 2024 • 4 minutes readOpenText World Europe 2024 has taken flight
AI: Elevating human potential
April 15, 2024 • 5 minutes readElevate human potential with Cloud Editions (CE) 24.2
Latest innovations revealed at OpenText World Europe 2024
April 15, 2024 • 10 minutes readWhat is new for OpenText Developer
Building faster and smarter with OpenText Thrust Studio – Early access program
April 15, 2024 • 4 minutes readReimagine work with Cloud Editions 24.1
We, at OpenText, are leading the charge in innovative digital transformation, equipping our customers with essential tools to tackle today’s most complex business challenges. The…
January 23, 2024 • 8 minutes readHow green is your application delivery software?
Sustainability is a growing priority for businesses and customers alike. As companies focus on their sustainability and environmental social governance (ESG) impacts, the IT landscape…
April 22, 2024 • 3 minutes readNext-gen developer experience
Greetings from Goose, a trusted partner for your AI journey. This AI-generated goose has been the champion of seven-star experiences, and over the last few…
April 19, 2024 • 5 minutes readTake productivity to new heights with AI-assisted DevOps
Gain insight faster and accelerate work with a powerful AI-assisted chat agent at your fingertips, powered by next-generation LLM.
April 15, 2024 • 3 minutes readThe Mainframe Turns 60: A Milestone in Computing History
Time Flies: Celebrating 60 Years of the Mainframe
March 21, 2024 • 6 minutes readOpenText Introduces New ‘COBOL Webinar Wednesdays’ Series
If mainframe and COBOL are at the heart of your operations, breaking the bounds of mainframe architecture to scale and innovate at speed can seem…
January 23, 2024 • 4 minutes readMainframe Modernization: Should I Stay, or Should I Go?
Mainframes still matter today. According to IBM, 45 of the world’s top 50 banks run on IBM zSystems. Furthermore, mainframes are used by 71% of…
January 19, 2024 • 4 minutes readIoT: Living at the edge
Greetings from Viper, trusted partner for your AI journey. This AI-generated hummingbird has been busy buzzing around in the clouds, figuring out how companies can…
April 19, 2024 • 4 minutes readElevate human potential with Cloud Editions (CE) 24.2
Latest innovations revealed at OpenText World Europe 2024
April 15, 2024 • 10 minutes readWhat’s new in OpenText Business Network Cloud
The latest announcement by OpenText of Cloud Editions includes exciting updates to the OpenText™ Business Network Cloud. Check out the latest updates below. April 2024:…
April 15, 2024 • 3 minutes readWhat’s new in OpenText Core Content
OpenText™ Core Content is a fast-deploying cloud content management solution that delivers simple, agile and secure cloud-based content management. It integrates into crucial business process…
April 19, 2024 • 9 minutes readElevate human potential with Cloud Editions (CE) 24.2
Latest innovations revealed at OpenText World Europe 2024
April 15, 2024 • 10 minutes readOpenText named a top player in Radicati 2024 Information Archiving Market Quadrant
Radicati’s Market Quadrant 2024 is a comprehensive report that evaluates the strengths and weaknesses of the leading vendors in the information archiving space.
April 08, 2024 • 2 minutes readWhat’s new in OpenText Core Content
OpenText™ Core Content is a fast-deploying cloud content management solution that delivers simple, agile and secure cloud-based content management. It integrates into crucial business process…
April 19, 2024 • 9 minutes readAI: Elevate human potential
ICE can show you the way to maximize the value of your data
April 15, 2024 • 3 minutes readElevate human potential with Cloud Editions (CE) 24.2
Latest innovations revealed at OpenText World Europe 2024
April 15, 2024 • 10 minutes readGoing green with cloud fax
Transforming communication for a sustainable future
April 22, 2024 • 2 minutes readElevate human potential with Cloud Editions (CE) 24.2
Latest innovations revealed at OpenText World Europe 2024
April 15, 2024 • 10 minutes readDrive customer success with OpenText Experience Cloud 24.2
Customers are at the heart of every thriving business.
April 15, 2024 • 4 minutes readGoing green with cloud fax
Transforming communication for a sustainable future
April 22, 2024 • 2 minutes readExceptional patient experiences start with smarter data
HIPAA taught us important lessons on how we interact with healthcare data, but it was a global pandemic that forced us to collectively go to…
February 28, 2024 • 3 minutes readHow digital fax and capture are transforming healthcare
Every second, an exponential amount of healthcare data is created and mined for valuable insights. A staggering 30% of the world’s data volume is currently…
February 15, 2024 • 4 minutes readElevate human potential with Cloud Editions (CE) 24.2
Latest innovations revealed at OpenText World Europe 2024
April 15, 2024 • 10 minutes readWhat’s new in OpenText Axcelerate
The latest announcement by OpenText of Cloud Editions includes some great updates to OpenText™ Axcelerate™. Check out the latest updates below. January 2024: What’s new…
January 31, 2024 • 20 minutes readThe evolving role of general counsel: Securing a seat at the table
Technological, social, and economic events have changed the legal and regulatory landscape. There was a time when in-house legal departments and the general counsel had…
January 17, 2024 • 7 minutes readGoing green with cloud fax
Transforming communication for a sustainable future
April 22, 2024 • 2 minutes readOpenText World Europe 2024 has taken flight
AI: Elevating human potential
April 15, 2024 • 5 minutes readElevate human potential with Cloud Editions (CE) 24.2
Latest innovations revealed at OpenText World Europe 2024
April 15, 2024 • 10 minutes readElevate human potential with Cloud Editions (CE) 24.2
Latest innovations revealed at OpenText World Europe 2024
April 15, 2024 • 10 minutes readWhat’s new in OpenText Business Network Cloud
The latest announcement by OpenText of Cloud Editions includes exciting updates to the OpenText™ Business Network Cloud. Check out the latest updates below. April 2024:…
April 15, 2024 • 3 minutes readDitch one-size-fits-all: OpenText offers customizable Microsoft Dynamics 365 EDI integration
A Microsoft-certified Dynamics 365 adapter delivers reliable on-time and on-budget EDI integration, surpassing inflexible alternative solutions
April 10, 2024 • 3 minutes readAutonomous cloud operations
Greetings from Skye, a trusted partner for your AI journey. This AI-generated llama has been living in the clouds, creating her own cloud trails to…
April 19, 2024 • 3 minutes readElevate human potential with Cloud Editions (CE) 24.2
Latest innovations revealed at OpenText World Europe 2024
April 15, 2024 • 10 minutes readBoost service desk agent productivity with GenAI that suggests solutions
OpenText IT Operations Aviator helps service desk agents quickly assess incoming tickets and resolve them faster.
April 15, 2024 • 3 minutes readMachine vs. machine
Greetings from Mav, trusted partner for your AI journey. This AI-generated moose has been on the hunt for threats and keeping security top of mind….
April 19, 2024 • 4 minutes readElevate human potential with Cloud Editions (CE) 24.2
Latest innovations revealed at OpenText World Europe 2024
April 15, 2024 • 10 minutes readTransforming digital forensic investigations
In the modern landscape of digital forensics, investigators must navigate many challenges stemming from the exponential growth of digital data.
April 15, 2024 • 4 minutes readStay in the loop!
Get our most popular content delivered monthly to your inbox.