If your archiving strategy equates to just “ARCHIVE EVERYTHING”, you may be exposing your company to more risk than you’re mitigating
In the digital age, your information and content can be as valuable as currency if managed correctly. Enterprise content – email, audio, text messages/SMS, tweets, and other social media posts – in collaboration with analytical tools can help you identify competitive opportunities (i.e. consumer insights) or mitigate risks pre-emptively. Many organizations with ad-hoc ECM strategies and information governance policies have been struggling with managing the vast amounts of content they are creating. Rather than just storing gigabytes of content, organizations must maintain content architecture and governance models (i.e. information management, archiving, and ECM strategies) that support (and capitalize!) on their competitive differentiators. Whether you’re a bank, a government, a CPG firm, a services firm, or any other organization – to be the best at what you do requires the right information, at the right time, and in the right format.
On the other hand, failing to manage your digital information and content correctly presents enormous risk to the organization. And that could potentially impact the integrity of your business. For example, eDiscovery is, and continues to be, a driving force behind information management initiatives for many organizations. Whether the source of legal investigation is litigation-based, a regulatory review, or an internal audit/investigation, ad-hoc eDiscovery processes, information governance policies, or content archiving strategies can leave the organization exposed to significant in the form of excessive legal fees and penalties. As a result, many IT departments have been spurred into reactive archiving as part of their overall Enterprise Content Management (ECM) strategies. Their solutions are typically comprised of on-premise electronic content archives that store all of their electronic communication and content. But in their haste to retain content in an effort to avoid the penalties of failure to produce these digital assets, many have unwittingly opened the door to a corresponding, or some might argue, even greater level of risk.
What are the components of an effective Enterprise Content Management strategy?
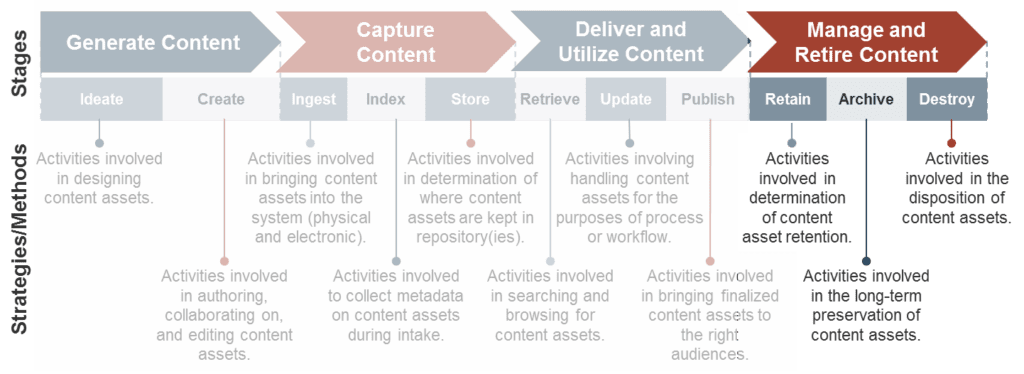
Archiving electronic communications and other content is only half of the battle; many content architects forget the importance of aligning manage and retire content activities and policies (retention, archival, disposition and destruction of content) methodologies and policies (see figure below). In the well-documented DuPont retrospective case study (Information Management Cost Reduction Strategies for Litigation), it was determined that during nine eDiscovery investigations, DuPont’s attorneys analyzed over 75 million pages of content with only 11 million pages actually being relevant to the cases. This incurred significant and unnecessary legal fees (nearly $12M USD) that could have been avoided if smart tagging and retention, disposition and destruction policies were followed accordingly. This example clearly demonstrates how ECM strategies must go beyond creating, capturing, and archiving content to optimize the findability and delivery of the right information assets at the right time and in the right format.
 Additionally, during the DuPont eDiscovery investigations, over 50% of the pages (over 38M) returned during eDiscovery searches were beyond the documented retention period and should not have been available to analyze at all. There is a widespread misconception that archiving everything will help reduce litigation, regulation, and internal risks. This misconception is further amplified by the commonly held belief that vast quantities of data can be used to unlock unique business value through the application of analytical and big data tools. However, according to the Compliance, Governance and Oversight Council, it is estimated that over 69% of archived organizational content is debris (whether redundant, obsolete or trivial) that could be and should be disposed of, and only 25% of archived data actually carried real business potential (Compliance, Governance and Oversight Council Summit, 2012).
Additionally, during the DuPont eDiscovery investigations, over 50% of the pages (over 38M) returned during eDiscovery searches were beyond the documented retention period and should not have been available to analyze at all. There is a widespread misconception that archiving everything will help reduce litigation, regulation, and internal risks. This misconception is further amplified by the commonly held belief that vast quantities of data can be used to unlock unique business value through the application of analytical and big data tools. However, according to the Compliance, Governance and Oversight Council, it is estimated that over 69% of archived organizational content is debris (whether redundant, obsolete or trivial) that could be and should be disposed of, and only 25% of archived data actually carried real business potential (Compliance, Governance and Oversight Council Summit, 2012).
Why should I care about excessive content retention
Excessive information storing exposes the organization to new liabilities and risks that can incur both financial and/or reputational impacts. For example, once a litigation action is initiated against an organization, most jurisdictions enforce laws (variable by jurisdiction) that prohibit the destruction of any content that may be relevant to the case under investigation. In this scenario, an organization that stores excessive information subjects itself to a whole new level of risk by enabling the evaluation of additional evidence by the antagonist. Additional risks and liabilities caused by excessive information retention include:
-
- Expensive archive storage and resource management to retain extraneous and expired content
- Cumbersome eDiscovery process (and costs) due to content volume and variety of sources (silos) of documentation and associated with increased labour costs during investigations
- Regulatory infractions as a result of sensitive documentation retained that should have been destroyed
- Discovery of further incriminating content that should have been and/or could have been deleted
- Potential threat of cybersecurity breach impacting confidentiality of sensitive communications
- Reduced business productivity as a result of poor indexing and extensive and exhausting content searches
In the face of expansive content growth, failing to manage your content properly is a recipe for disaster and is no longer a viable option. In order to mitigate risks associated with excessive content retention, organizations must consider the consequences of these risks, and align their archives accordingly. Tune into Info-Tech’s upcoming blogs to learn about the consequences of excessive content retention, identify how to mitigate risks and create an aligned archiving and ECM strategy that considers organizational objectives, compliance mandates, and risk appetite.
About the Author
Ryan Smith is an Associate Research Director in Info-Tech’s Enterprise Content Management (ECM) Advisory Practice specializing in the development, establishment, and governance of ECM strategies. Ryan regularly provides IT and business leaders with guidance, analysis, and tools required to optimize their ECM operations and unlock the true power of content as a business enabler. His client work includes developing strategic visions and roadmaps, requirements gathering and vendor evaluation, and the establishment of governance bodies including ECM centers of excellence. He is the author of Info-Tech’s ECM Strategy Development Framework which outlines the seven sub-disciplines of ECM and serves as the foundational methodology of Info-Tech’s ECM Practice.

About Retain by Micro Focus
Micro Focus Retain provides archiving of email, social media, and mobile communication data. Retain archives all of this data into one central archive. Retain includes built-in eDiscovery tools, including browse, search, litigation holds, export, print, forward, and redaction archived data. Policy-based archiving ensures that you only keep what you need to keep, based on age of a message, mailbox, or post office. Once a message reaches the specified age for deletion, it is automatically removed from the archive. Retain allows you to manage and have oversight on your email, social media, and mobile communication data.
To see how Retain can work for you, or to get a price quote, visit www.RetainArchiving.com